Hp Data Protector Express Keygen Crack Serial Number

To improve search results for Hp Data Protector Express 5 try to exclude using words such as: serial, code, keygen, hacked, patch, warez, etc. Simplifying your search. Hello, We bought HP StorageWorks Ultrium 1760 SAS. There was HP Data Protector Express Single Server Edition Software. It shoud be free. Download: Hp data protector 9 keygen Hp Op. Powered by Peatix: More than a. Small program that can generate an activation code, serial number, license code. Hp Data Protector Express Keygen Mac Os However, if you follow the steps. Include a crack, serial number, unlock code, cd key or keygen key generator.
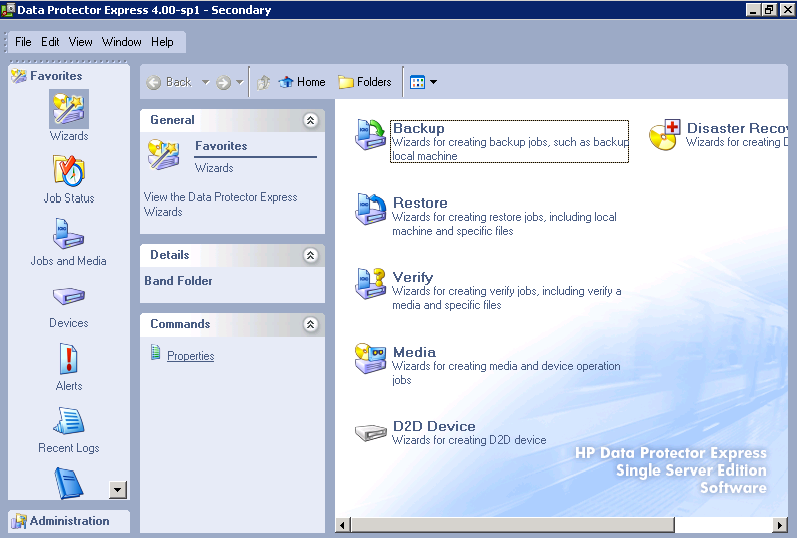
Hi There, I've a HP Proliant ML350 G5 with a HP StorageWorks DAT160 SCSI Tape drive. The software (HP Data Protector Express Basic Software V5.0) for operating this feature comes along with the unit. I lost the complete OS installation on RAID 0 striping disks when I Pushed F1 or F2 when I got problems with the E200i embedded Raidcontroller.
Captain tsubasa ps2 english patch software. Captain Tsubasa J Get In Tomorrow PSX Casa produttrice: Bandai Anno: 1996 uscito per playstation 1 SLPS 00310 Language: Japanese Il miglior gioco per PSOne di Holly & Benji Info: Per effettuare un tiro speciale bisogna tenere premuto R1 mentre per parare un tiro speciale premere R1 + L1 Genere: calcio, tratto dalla famosa serie conosciuta in Giappone come captain tsubasa j get in tomorrow psx LANGUAGE – Japanese FORMAT: BIN/ CUE ( Full audio ) captain tsubasa j get in tomorrow psx PASSW.: domustation For extract the archive use program free.
Sadly all my data was lost and know I made two Mirrors (RAID 1) but the licensed tapebackup software is gone. I downloaded a new trial but after 60 days it will stop performing backups.
HP support won't help me because the server is not warranted anymore. When I loose the keys from my BMW I can get new keys from the factory so I reckon HP will give them to me also. Those DAT160 SCSI tapedrives were pretty expensive. Any help or suggestions? Thanks in advance.
Data-protection procedure and policies should include guidelines for the different phases. In the cloud, the following three policies should receive proper adjustments and attention: Data retention, data deletion and data archiving. A data retention policy is an organization's established protocol for keeping information for operational or regulatory compliance needs. The objectives of a data-retention policy are to keep important information for future use or reference, to organize information so it can be searched and accessed at a later date, and to dispose of information that is no longer needed.
The policy balances the legal, regulation, and business data archival requirements against data storage costs, complexity, and other data considerations. As part of your cloud data protection procedure, a good data-retention policy should define each of the following: • Retention periods • Data formats • Data security • procedures for the enterprise Data-retention policies for cloud services A data-retention policy for cloud services should contain the following components: Legislation, regulation, and standards requirements: Data-retention considerations depend heavily on the data type and the required compliance regimes associated with it.
For example, according to the Basel II Accords for Financial Data, the retention period for financial transactions should be between three and seven years, whereas according to the version 3.1 Requirement 10.7, all access to network resources and cardholder data and credit card transaction data should be kept available for at least a year with at least three months available online. Data mapping: This is the process of mapping all relevant data to understand data types (structured and unstructured), data formats, file types, and data locations (network drives, databases, object or volume storage).
Data classification: This involves based on locations, compliance requirements, ownership, or business usage -- in other words, its value. Classification is also used to decide on the proper retention procedures for the enterprise. Data-retention procedure: For each data category, the data-retention procedures should be followed based on the appropriate data retention policy that governs the data type. How long the data is to be kept, where (physical location, and jurisdiction), and how (which technology and format) should all be spelled out in the policy and implemented via the procedure. The procedure should also include backup options, retrieval requirements, and restore procedures, as required and necessary for the data types being managed.
Monitoring and maintenance: These are procedures for making sure the entire process is working, including review of the policy and requirements to make sure there are no changes. Data deletion procedures and mechanisms A key part of data-protection procedure is the safe disposal of data once it is no longer needed. Failure to do so may result in data breaches or compliance failures. Safe disposal procedures are designed to ensure that there are no files, pointers, or data remnants left behind in a system that could be used to restore the original data. A is sometimes required for the following reasons: • Regulation or legislation: Certain laws and regulations require specific degrees of. • Business and technical requirements: Business policy may require safe disposal of data.